|
|
| Sum (int id) |
| |
| virtual void | Draw (wxPoint2DDouble translation, double scale) const |
| | Draw the element. More...
|
| |
| virtual bool | Contains (wxPoint2DDouble position) const |
| | Checks if the element contains a position. More...
|
| |
| virtual bool | Intersects (wxRect2DDouble rect) const |
| | Check if the element's rect intersects other rect. More...
|
| |
| virtual bool | ShowForm (wxWindow *parent, Element *element) |
| | Show element data form. More...
|
| |
| virtual void | Rotate (bool clockwise=true) |
| | Rotate the element. More...
|
| |
|
virtual std::vector< Signal > | GetSignalList () const |
| |
|
virtual void | SetSignalList (std::vector< Signal > signalList) |
| |
|
virtual bool | Solve (double *input, double timeStep) |
| |
|
virtual void | UpdatePoints () |
| |
|
void | AddInNode () |
| |
|
void | RemoveInNode () |
| |
|
virtual rapidxml::xml_node * | SaveElement (rapidxml::xml_document<> &doc, rapidxml::xml_node<> *elementListNode) |
| |
|
virtual bool | OpenElement (rapidxml::xml_node<> *elementNode) |
| |
| virtual Element * | GetCopy () |
| | Get a the element copy. More...
|
| |
|
| ControlElement (int id) |
| |
| virtual void | StartMove (wxPoint2DDouble position) |
| | Update the element attributes related to the movement. More...
|
| |
| virtual void | Move (wxPoint2DDouble position) |
| | Move the element other position. More...
|
| |
|
void | SetNodeList (std::vector< Node *> nodeList) |
| |
|
std::vector< Node * > | GetNodeList () const |
| |
|
virtual void | DrawNodes () const |
| |
|
virtual void | ReplaceNode (Node *oldNode, Node *newNode) |
| |
| virtual bool | UpdateText () |
| | Update the OpenGL text in the element (if present). More...
|
| |
|
virtual bool | IsSolved () const |
| |
|
virtual void | SetSolved (bool solved=true) |
| |
|
virtual bool | Initialize () |
| |
|
virtual double | GetOutput () const |
| |
|
virtual void | SetOutput (double output) |
| |
|
| Element () |
| | Constructor.
|
| |
|
virtual | ~Element () |
| | Destructor.
|
| |
| void | SetDragging (bool dragging=true) |
| | Set if the element are being dragged. More...
|
| |
| void | SetHeight (double height) |
| | Set element height. More...
|
| |
| void | SetPosition (const wxPoint2DDouble position) |
| | Set the element position and update the rectangle. More...
|
| |
| void | SetSelected (bool selected=true) |
| | Set element selection. More...
|
| |
| void | SetWidth (double width) |
| | Set element width. More...
|
| |
| void | SetAngle (double angle) |
| | Set element angle. More...
|
| |
| void | ShowPickbox (bool showPickbox=true) |
| | Set if the pickbox is shown. More...
|
| |
| void | SetBorderSize (double borderSize) |
| | Set the size of the border (shown in selected elements). More...
|
| |
| bool | SetOnline (bool online=true) |
| | Set if the element is online or offline. More...
|
| |
| virtual void | SetPointList (std::vector< wxPoint2DDouble > pointList) |
| | Set the list of points that connect the element to the bus. More...
|
| |
| wxRect2DDouble | GetRect () const |
| | Get the element rectangle. More...
|
| |
| wxPoint2DDouble | GetPosition () const |
| | Get the element position. More...
|
| |
| bool | IsDragging () const |
| | Checks if the element is being dragged. More...
|
| |
| double | GetHeight () const |
| | Get the element height. More...
|
| |
| bool | IsSelected () const |
| | Checks if the element is selected. More...
|
| |
| double | GetWidth () const |
| | Get the element width. More...
|
| |
| double | GetAngle () const |
| | Get the element angle. More...
|
| |
| double | GetRotationAngle () const |
| | Get the angle of rotation. More...
|
| |
| bool | IsPickboxShown () const |
| | Checks if the pickbox is shown. More...
|
| |
| bool | IsOnline () const |
| | Checks if the element is online or offline. More...
|
| |
| virtual std::vector< wxPoint2DDouble > | GetPointList () const |
| | Get the list of points that connect the element to bus. More...
|
| |
| virtual bool | AddParent (Element *parent, wxPoint2DDouble position) |
| | Add a parent to the element. This method must be used on power elements that connect to a bus, so the parent must be a bus. The element basic points are calculated in this method, so apply this when the element is being inserted. More...
|
| |
| virtual void | AddParent (Element *parent) |
| | Add a parent to the element. More...
|
| |
| virtual void | SetID (int id) |
| | Set the element ID. More...
|
| |
| virtual int | GetID () const |
| | Get the element ID. More...
|
| |
| virtual void | AddChild (Element *child) |
| | Add a child to the child list. More...
|
| |
| virtual void | RemoveChild (Element *child) |
| | Remove a child from the list. More...
|
| |
| virtual void | ReplaceChild (Element *oldChild, Element *newChild) |
| | Replace a child from the list. More...
|
| |
| virtual wxString | GetTipText () const |
| | Get the tip text. More...
|
| |
| virtual bool | GetContextMenu (wxMenu &menu) |
| | Get the element contex menu. More...
|
| |
| virtual void | AddPoint (wxPoint2DDouble point) |
| | Add point to the list of points that connect the element to the bus. More...
|
| |
| virtual void | MoveNode (Element *parent, wxPoint2DDouble position) |
| | Move a node. StartMove(wxPoint2DDouble position) before start moving. More...
|
| |
| virtual bool | NodeContains (wxPoint2DDouble position) |
| | Check if a node contains a point. If contains, set the attributes related to node movement. More...
|
| |
|
virtual void | UpdateNodes () |
| | Update the nodes according to the parents. If a parent is removed, use this method.
|
| |
| virtual bool | SetNodeParent (Element *parent) |
| | Set a perent to the node. If all conditions are met, a new parent are added to the element and the points related to the nodes will be calculated. More...
|
| |
| virtual void | RemoveParent (Element *parent) |
| | Remove a parent. More...
|
| |
| virtual void | ReplaceParent (Element *oldParent, Element *newParent) |
| | Replace a parent. More...
|
| |
| virtual void | RotateNode (Element *parent, bool clockwise=true) |
| | Rotate a node. More...
|
| |
| virtual bool | PickboxContains (wxPoint2DDouble position) |
| | Check if a pickbox contains a point. If contains the attributes related to pickbox movement will be calculated. More...
|
| |
| virtual void | MovePickbox (wxPoint2DDouble position) |
| | Move the pickbox. More...
|
| |
| virtual wxCursor | GetBestPickboxCursor () const |
| | Get the best cursor to shown to the user when the mouse is above a pickbox. More...
|
| |
|
virtual void | ResetPickboxes () |
| | Remove the pickboxes.
|
| |
|
virtual void | ResetNodes () |
| | Remove the active nodes.
|
| |
| virtual wxPoint2DDouble | WorldToScreen (wxPoint2DDouble translation, double scale, double offsetX=0.0, double offsetY=0.0) const |
| | Convert the element position to screen position. More...
|
| |
| virtual wxPoint2DDouble | WorldToScreen (wxPoint2DDouble position, wxPoint2DDouble translation, double scale, double offsetX=0.0, double offsetY=0.0) const |
| | Convert a generic position to screen position. More...
|
| |
| virtual bool | RotatedRectanglesIntersects (wxRect2DDouble rect1, wxRect2DDouble rect2, double angle1, double angle2) const |
| | Check if two roteted rectangles intersect. More...
|
| |
| virtual void | DrawCircle (wxPoint2DDouble position, double radius, int numSegments, GLenum mode=GL_LINE_LOOP) const |
| | Draw a circle. More...
|
| |
|
virtual void | DrawArc (wxPoint2DDouble position, double radius, double initAngle, double finalAngle, int numSegments, GLenum mode=GL_LINE_LOOP) const |
| |
| virtual void | DrawRectangle (wxPoint2DDouble position, double width, double height, GLenum mode=GL_QUADS) const |
| | Draw rectangle. More...
|
| |
| virtual void | DrawRectangle (wxPoint2DDouble *points, GLenum mode=GL_QUADS) const |
| | Draw rectangle. More...
|
| |
| virtual void | DrawTriangle (std::vector< wxPoint2DDouble > points, GLenum mode=GL_TRIANGLES) const |
| | Draw a triangle. More...
|
| |
| virtual void | DrawPoint (wxPoint2DDouble position, double size) const |
| | Draw a point. More...
|
| |
| virtual void | DrawLine (std::vector< wxPoint2DDouble > points, GLenum mode=GL_LINE_STRIP) const |
| | Draw line. More...
|
| |
| virtual void | DrawPickbox (wxPoint2DDouble position) const |
| | Draw pickbox. More...
|
| |
| virtual wxPoint2DDouble | RotateAtPosition (wxPoint2DDouble pointToRotate, double angle, bool degrees=true) const |
| | Rotate a point as element position being the origin. More...
|
| |
| virtual std::vector< Element * > | GetParentList () const |
| | Get the parent list. More...
|
| |
| virtual std::vector< Element * > | GetChildList () const |
| | Get the Child list. More...
|
| |
| virtual void | CalculateBoundaries (wxPoint2DDouble &leftUp, wxPoint2DDouble &rightBottom) const |
| | Calculate the element boundaries. More...
|
| |
| virtual void | GeneralMenuItens (wxMenu &menu) |
| | Insert general itens to context menu. More...
|
| |
| virtual double | PointToLineDistance (wxPoint2DDouble point, int *segmentNumber=NULL) const |
| | Calculate the distance between a line (formed by point list) and a point. More...
|
| |
|
void | SaveCADProperties (rapidxml::xml_document<> &doc, rapidxml::xml_node<> *elementNode) |
| |
|
bool | OpenCADProperties (rapidxml::xml_node<> *elementNode) |
| |


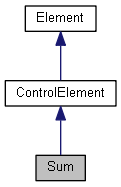
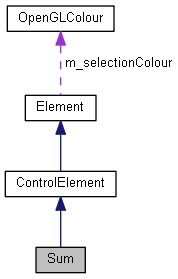
 Public Member Functions inherited from ControlElement
Public Member Functions inherited from ControlElement Public Member Functions inherited from Element
Public Member Functions inherited from Element Protected Attributes inherited from ControlElement
Protected Attributes inherited from ControlElement Protected Attributes inherited from Element
Protected Attributes inherited from Element Static Public Member Functions inherited from ControlElement
Static Public Member Functions inherited from ControlElement Static Public Member Functions inherited from Element
Static Public Member Functions inherited from Element Protected Member Functions inherited from ControlElement
Protected Member Functions inherited from ControlElement 1.8.13
1.8.13